Author: Frank, PANews
A single on-chain transaction, costing less than $0.1, is capable of instantly obliterating tens of thousands of dollars worth of market-making orders from Polymarket’s order book. This isn’t a theoretical exploit; it’s a stark reality unfolding right now.
In February 2026, a novel attack vector targeting Polymarket market makers was exposed on social media. Blogger BuBBliK aptly described it as “elegant & brutal” due to its deceptive simplicity and devastating impact. Attackers can execute an entire cycle of this exploit in approximately 50 seconds, incurring Gas fees of less than $0.1 on the Polygon network. The victims, primarily market makers and automated trading bots with substantial capital committed to their orders, face the destruction of their active orders and significant, often passive, financial losses.
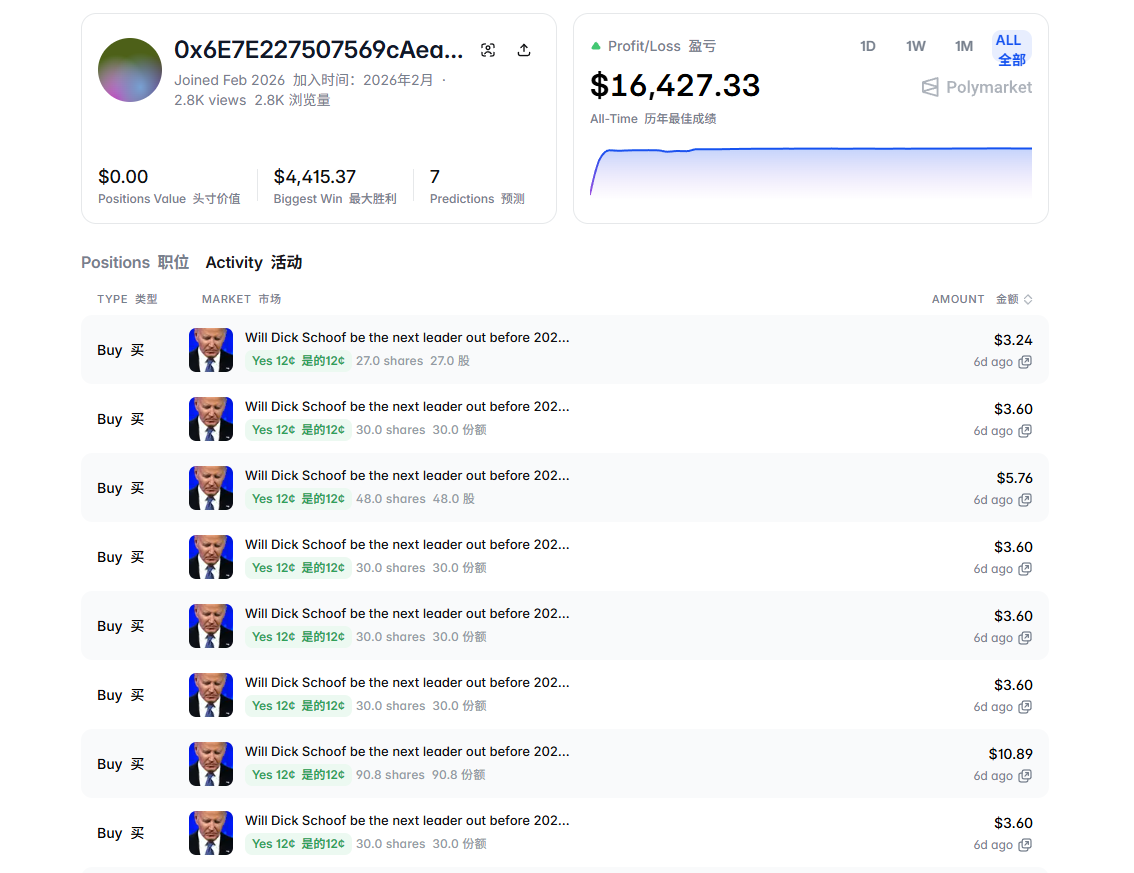
PANews investigated an attacker’s address flagged by the community. Registered in February 2026, this account participated in only seven markets yet amassed a total profit of $16,427. Crucially, the bulk of these earnings were realized within a single day. The fact that a prediction market leader, valued at an estimated $9 billion, can have its foundational liquidity undermined by an exploit costing mere cents reveals a vulnerability far deeper than a simple technical glitch.
PANews delves into the technical mechanics, economic rationale, and the profound implications of this attack for the broader prediction market industry.
The Anatomy of the Attack: A Precision Strike Exploiting a Temporal Gap
To grasp the essence of this exploit, one must first understand Polymarket’s unique transaction architecture. Unlike most decentralized exchanges (DEXs), Polymarket employs a hybrid “off-chain matching + on-chain settlement” model. This design aims to deliver a user experience akin to centralized exchanges, featuring zero Gas fees for placing orders and near-instantaneous off-chain matching. However, this convenience introduces a critical “time difference” – a window of several to over ten seconds – between the off-chain matching and the final on-chain settlement. It is precisely this temporal gap that attackers exploit.
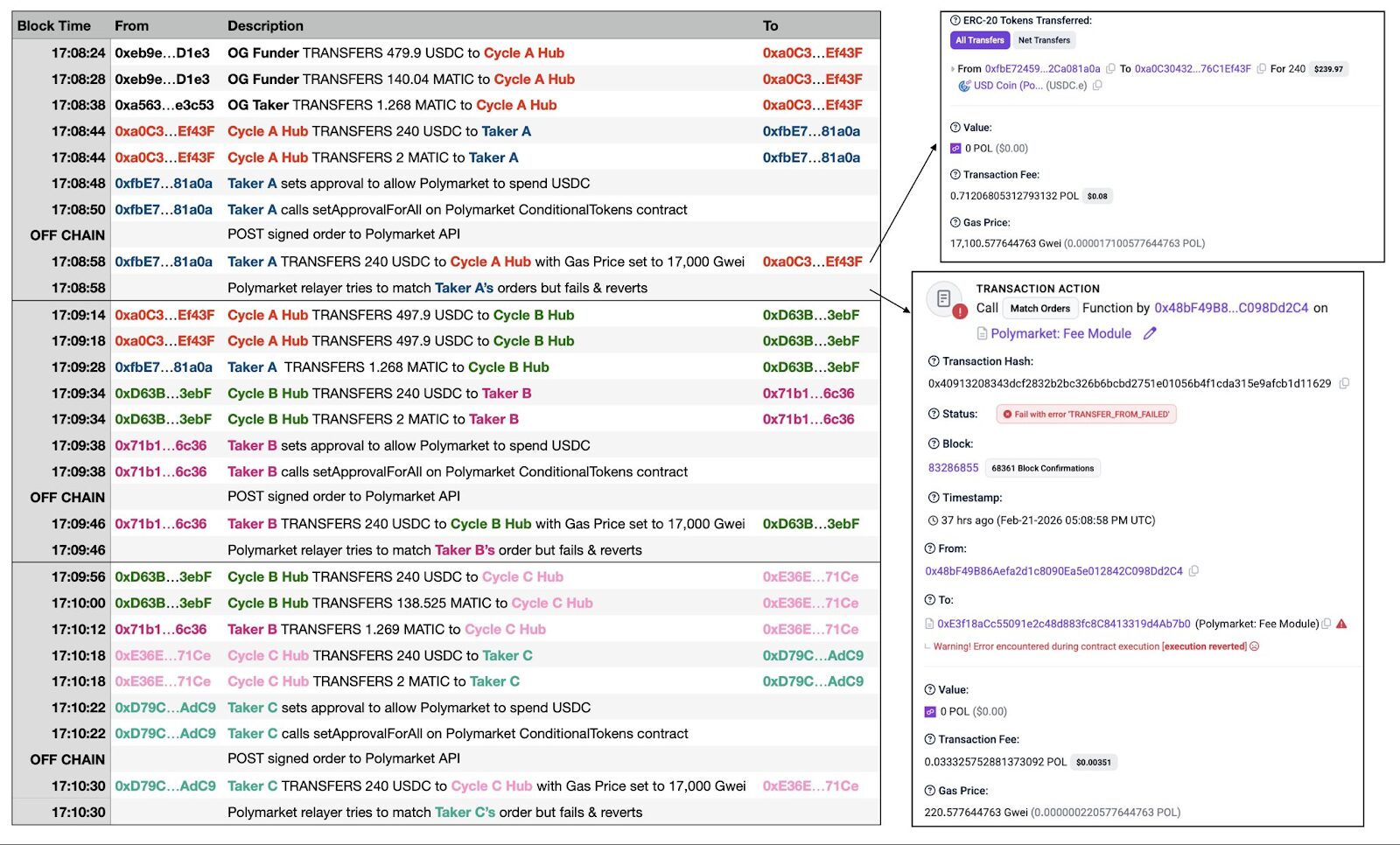
The attack’s core logic is surprisingly straightforward. The attacker initiates a standard buy or sell order via API. The off-chain system processes this order, verifies the signature and balance, and proceeds to match it against existing market maker orders in the order book. Almost simultaneously, however, the attacker broadcasts a separate USDC transfer on the Polygon chain with an extremely high Gas fee, effectively draining their wallet of all funds. Due to the elevated Gas fee, this “wallet-draining” transaction is confirmed by the network well before Polymarket’s relay can submit the matched order for on-chain settlement. By the time the relay attempts to execute the settlement, the attacker’s wallet is empty, causing the transaction to fail and roll back due to insufficient funds.
If the story ended there, the only loss would be a minor Gas fee for the relay. But the truly devastating consequence is this: despite the on-chain transaction failing, Polymarket’s off-chain system forcibly removes all innocent market maker orders that were part of that failed match from the order book. In essence, the attacker uses a transaction guaranteed to fail to “one-click clear” legitimate buy and sell orders placed by others with real capital.
Consider an analogy: it’s like an individual shouting a high bid at an auction, only to declare “I have no money” the moment the hammer falls. Yet, instead of simply voiding that bid, the auction house confiscates all other legitimate bidders’ paddles, causing the entire auction to collapse.
The community has since identified an “upgraded version” of this attack, dubbed “Ghost Fills.” This variant eliminates the need for a front-run transfer. Instead, after an order is matched off-chain but before on-chain settlement, the attacker directly invokes the contract’s “cancel all orders” function, instantly invalidating their own order and achieving the same outcome. Even more cunningly, attackers can place orders across multiple markets simultaneously, monitor price movements, and only allow favorable orders to settle normally, while canceling unfavorable ones using this method – effectively creating a “win-only” free option.
Attack Economics: From Cents to Thousands in Profit
Beyond directly clearing market maker orders, this state desynchronization between off-chain and on-chain systems is also being leveraged to target automated trading robots. Monitoring by the GoPlus security team has identified several affected bots, including Negrisk, ClawdBots, and MoltBot.
While clearing orders or creating “ghost fills” doesn’t directly generate profit, the question remains: how do attackers monetize these actions?
PANews’ analysis reveals two primary profit pathways for the attackers:
- Monopolistic Market-Making Post-Liquidation: In a healthy, popular prediction market, multiple market makers compete, resulting in tight bid-ask spreads (e.g., a buy order at $0.49 and a sell order at $0.51). Market makers profit from these narrow spreads. The attacker repeatedly launches “doomed-to-fail” transactions, forcibly clearing all competing orders. This creates a vacuum in the order book, allowing the attacker to immediately place their own buy and sell orders with significantly widened spreads (e.g., a buy at $0.40 and a sell at $0.60). Users needing to trade, with no better options, are compelled to accept these inflated prices, enabling the attacker to capture substantial “monopoly spreads.” This cycle then repeats: clear, monopolize, profit, clear again.
- Hunting Hedging Bots: This pathway is more direct, focusing on “hunting hedging robots.” Consider an example: in a market where the “Yes” outcome is priced at $0.50, an attacker places a $10,000 “Yes” buy order with a market-making bot via API. The off-chain system confirms the match, and the API instantly informs the bot, “You have sold 20,000 shares of Yes.” To hedge its risk, the bot immediately buys 20,000 shares of “No” in a related market to lock in profit. However, the attacker then causes the initial $10,000 buy order to fail and roll back on-chain. This means the bot never actually sold any “Yes” shares. Its assumed hedging position is now a naked, one-sided bet, holding 20,000 shares of “No” without a corresponding short position for protection. The attacker then capitalizes on this by genuinely trading in the market, profiting either from the bot being forced to dump its unprotected positions or by arbitraging from the resulting market price shifts.
From a cost perspective, each attack cycle demands less than $0.1 in Polygon network Gas fees and takes approximately 50 seconds. Theoretically, this allows for around 72 attacks per hour. One attacker reportedly deployed a “dual wallet cycle system” (alternating between Cycle A Hub and Cycle B Hub) to achieve fully automated, high-frequency exploitation. Hundreds of failed transactions have already been recorded on-chain.
Regarding revenue, the community-flagged attacker address reviewed by PANews, registered in February 2026, participated in just seven markets but generated a total profit of $16,427, with the largest single gain reaching $4,415. The core profit-generating activities were concentrated within extremely short timeframes. This implies that for a total Gas cost potentially under $10, an attacker leveraged over $16,000 in profit within a single day. And this represents only one identified address; the actual number of attackers and total illicit gains could be significantly higher.
For the affected market makers, quantifying losses is even more challenging. Traders operating BTC 5-minute market bots on Reddit have reported losses amounting to “thousands of dollars.” The deeper damage extends to opportunity costs from frequently forced order removals and the operational overhead of continually adjusting market-making strategies.
A more troubling aspect is that this vulnerability stems from a fundamental design flaw within Polymarket’s underlying mechanism, making a quick fix improbable. As this attack method gains wider recognition, similar exploits are likely to proliferate, further eroding Polymarket’s already precarious liquidity.
Community Self-Help, Warnings, and Platform Silence
As of now, Polymarket’s official channels have remained silent, issuing no detailed statement or proposed fix for this order book attack. Users on social media have also voiced concerns that this bug was reported multiple times months ago, yet consistently ignored. This echoes Polymarket’s previous stance, where it declined to issue refunds following a “governance attack” involving UMA Oracle vote manipulation.
In the absence of official intervention, the community has taken matters into its own hands. A community developer independently created “Nonce Guard,” an open-source monitoring tool. This tool provides real-time surveillance of order cancellation operations on the Polygon chain, compiles blacklists of attacker addresses, and offers general warning signals for trading robots. However, this solution is essentially a reactive patch, strengthening monitoring rather than fundamentally resolving the underlying architectural vulnerability.
Compared to other arbitrage techniques, the potential ramifications of this attack are far more profound:
- For Market Makers: Their diligently maintained orders can be cleared in batches without warning, completely eroding the stability and predictability of their strategies. This could directly diminish their incentive to provide liquidity on Polymarket.
- For Automated Trading Bots: API-returned transaction signals become unreliable, rendering their operations highly risky.
- For Ordinary Users: They may experience significant losses due to instantaneously disappearing liquidity during their trades.
Ultimately, for the Polymarket platform itself, a scenario where market makers are hesitant to place orders and bots are unwilling to hedge will inevitably lead to a shrinking order book depth, intensifying a vicious cycle that threatens its very ecosystem.
(The above content is excerpted and reproduced with permission from our partner PANews. Original Link)
Disclaimer: This article provides market information only. All content and opinions are for reference only, do not constitute investment advice, and do not represent the views and positions of BlockBeats. Investors should make their own decisions and trades. The author and BlockBeats will not bear any responsibility for direct or indirect losses incurred by investors’ transactions.