By HIBIKI, CryptoCity
Unprecedented Breach: LiteLLM Supply Chain Attack Exposes Half a Million Credentials and Gigabytes of Data
LiteLLM, an open-source AI toolkit boasting an astounding 3.4 million daily downloads, serves as a vital conduit for developers connecting to various Large Language Models (LLMs). However, this indispensable tool recently became the target of a sophisticated cyberattack, sending shockwaves through the global software development and cloud communities.
Kaspersky estimates that this pervasive attack has jeopardized over 20,000 code repositories. The attackers boldly claim to have exfiltrated hundreds of gigabytes of confidential data and more than 500,000 user credentials, underscoring the severe implications for digital security worldwide.
In a startling revelation, cybersecurity experts tracing the origins of the LiteLLM incident discovered the initial vector to be Trivy – an open-source security scanning tool widely deployed by enterprises to identify system vulnerabilities. The irony of a security tool being weaponized against its users highlights a critical vulnerability in the software supply chain.
This incident exemplifies a classic “nested” supply chain attack, where threat actors target an upstream, trusted tool that their ultimate victim relies upon. By subtly injecting malicious code into this foundational component, the attackers effectively poisoned the well at its source, compromising all downstream users without their immediate knowledge.

The Domino Effect: Unpacking the LiteLLM Attack Chain from Security Tool to AI Toolkit
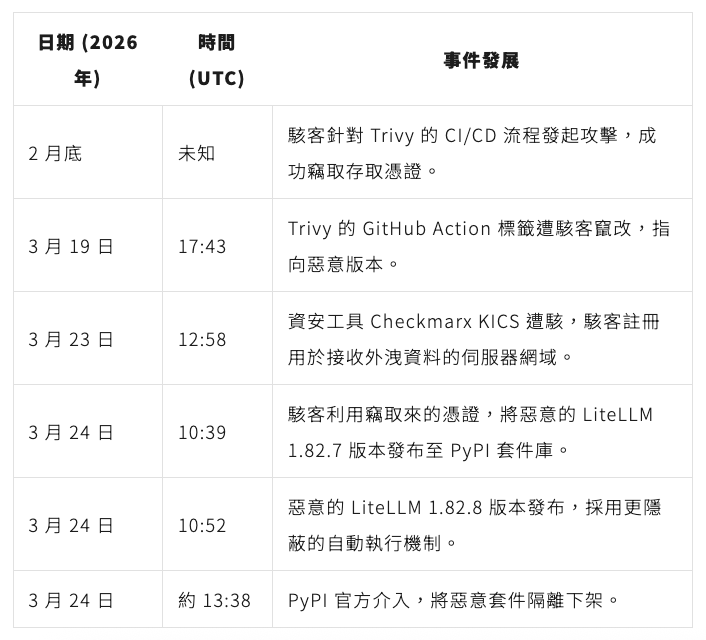
According to comprehensive analyses by cybersecurity firms Snyk and Kaspersky, the groundwork for the LiteLLM attack was laid as early as late February 2026.
The attackers exploited a vulnerability within GitHub’s CI/CD (Continuous Integration/Continuous Delivery) pipeline, a critical automation process for software testing and release. This breach allowed them to pilfer access tokens belonging to Trivy maintainers. Crucially, these compromised tokens were not fully revoked, enabling the attackers to tamper with Trivy’s release tags on March 19th. Consequently, automated deployment pipelines downloaded a version of the scanning tool that was secretly laced with malicious code.
Leveraging the same insidious methodology, the attackers gained control over LiteLLM’s publishing rights on March 24th, subsequently uploading compromised versions 1.82.7 and 1.82.8, which contained the embedded malware.
The covert operation was inadvertently exposed when developer Callum McMahon, while testing an extension for the Cursor editor, found his system automatically downloading the latest LiteLLM version. This immediately led to his computer’s resources being completely depleted. Through debugging with the assistance of an AI tool, McMahon discovered a critical flaw in the malicious code. This flaw accidentally triggered a “fork bomb”—a self-replicating malicious process designed to exhaust a computer’s memory and processing capabilities—thereby bringing the hidden attack to light prematurely.
Snyk’s analysis reveals that the malicious code deployed in this attack operated in three distinct stages:
- Data Collection: The malware systematically scoured the victim’s computer for highly sensitive information. This included SSH remote connection keys, access credentials for major cloud services like AWS and GCP, and critical cryptocurrency wallet seed phrases for assets such as Bitcoin and Ethereum.
- Encryption and Exfiltration: All collected data was then encrypted, bundled, and covertly transmitted to a deceptive domain pre-registered by the attackers, ensuring the stealthy extraction of valuable information.
- Persistence and Lateral Movement: The malicious program established backdoors within the compromised system. Furthermore, if it detected a Kubernetes environment—an open-source platform for automating the deployment and management of containerized applications—it would attempt to propagate the malware to all nodes across the entire cluster, aiming for widespread network compromise.
Key Milestones: The LiteLLM and Trivy Supply Chain Attack Timeline
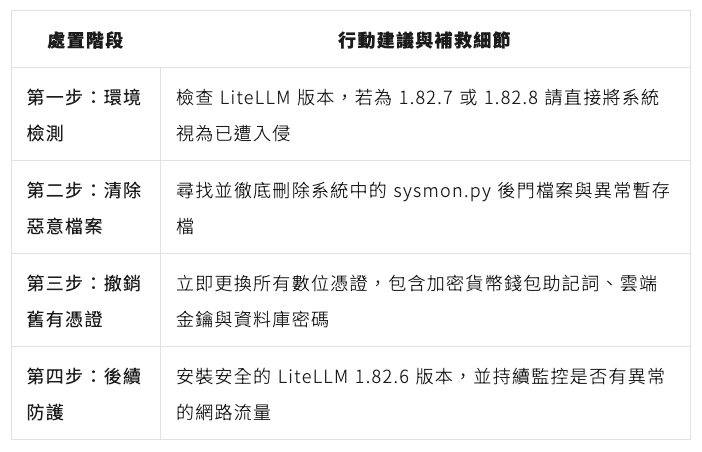
Urgent Call to Action: Detection and Remediation for Affected Systems
If you installed or updated the LiteLLM package after March 24, 2026, or if your automated development environment utilized the Trivy scanning tool, your system is at a high risk of compromise. Immediate action is imperative.
Based on recommendations from Callum McMahon and Snyk, the paramount tasks for protection and remediation involve accurately assessing the scope of the compromise and thoroughly neutralizing any established backdoors used by the attackers.
To bolster the security of GitHub Actions, Kaspersky advises integrating the following open-source tools:
- zizmor: A powerful tool designed for static analysis, specifically to detect misconfigurations and potential vulnerabilities within GitHub Actions workflows.
- gato and Gato-X: These tools are invaluable for identifying structurally vulnerable automated pipelines, helping to pinpoint weak points in your CI/CD processes.
- allstar: Developed by the Open Source Security Foundation (OpenSSF), this GitHub application is purpose-built to configure and rigorously enforce security policies across GitHub organizations and repositories, ensuring consistent security posture.
Beyond the Code: How Attackers Capitalized on AI Trends in the LiteLLM Breach
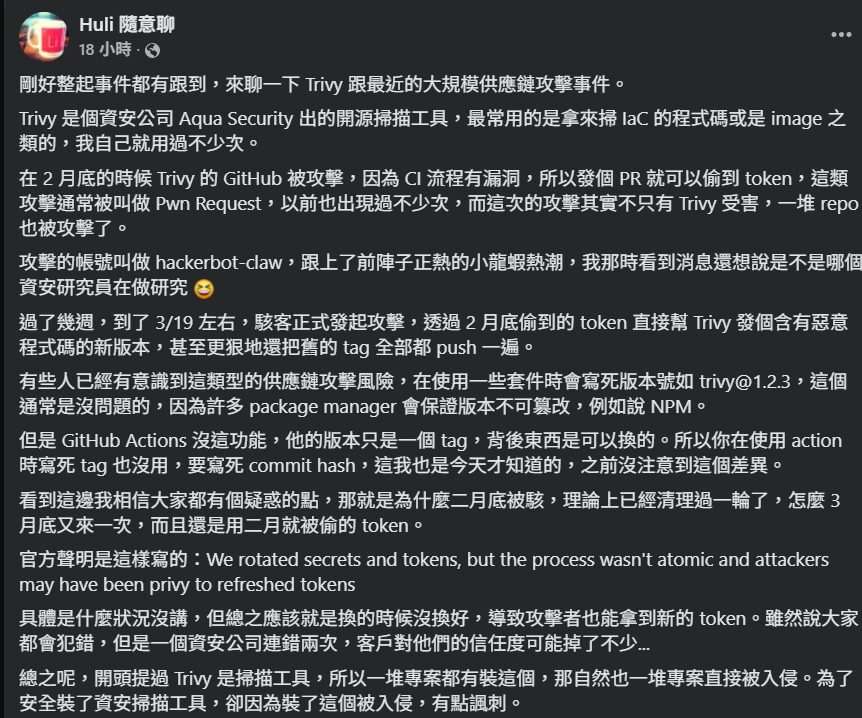
Analyses by Snyk and cybersecurity engineer Huli reveal that the sophisticated orchestrators behind this incident are a hacker collective known as TeamPCP. This group has been actively operating since December 2025, frequently establishing channels on communication platforms like Telegram to coordinate their illicit activities.
Huli highlighted a particularly cunning aspect of the attack: the hackers employed an automated attack component dubbed “hackerbot-claw.” This name is a deliberate and clever nod to the “OpenClaw” (or “lobster farming”) AI agent trend, which has recently garnered significant attention within the AI community. By aligning their attack nomenclature with a popular AI concept, TeamPCP demonstrated a keen awareness of current technological trends and a desire to blend into the digital landscape.
This group of attackers showcased remarkable organization and targeting precision, striking at high-privilege, widely used infrastructure tools like Trivy and LiteLLM. Their ability to leverage cutting-edge AI trends to amplify the scale and impact of their operations underscores a new level of sophistication in cybercrime.
As AI tools become increasingly ubiquitous, managing permissions and ensuring supply chain security within development processes are no longer optional but critical imperatives for all enterprises.
Recent incidents serve as stark warnings: from the compromise of prominent developers’ NPM accounts leading to malicious code injection into JavaScript packages—potentially impacting numerous DApps and crypto wallets—to Anthropic’s disclosure of Chinese hackers orchestrating the first large-scale AI-automated cyber espionage operation via Claude Code. These cases underscore the escalating threat landscape and the urgent need for robust security measures in the age of artificial intelligence.
(The above content is an authorized excerpt and reprint from our partner “CryptoCity”, original link.)
Disclaimer: This article is for market information purposes only. All content and views are for reference only and do not constitute investment advice. They do not represent the views or positions of BlockTempo. Investors should make their own decisions and trades. The author and BlockTempo will not bear any responsibility for direct or indirect losses incurred by investors’ transactions.