Author: Max, CryptoCity
From State Surveillance to Crypto Heist: The Alarming Evolution of the Coruna iOS Exploit Kit
A chilling report from Google’s Threat Intelligence Group (GTIG) reveals a significant and evolving threat to global iPhone users: the Coruna iOS exploit kit, also known as CryptoWaters. This sophisticated tool has undergone a dramatic transformation, evolving from a precision state-sponsored surveillance instrument into a formidable “asset harvester” designed to plunder digital wealth.
The Metamorphosis of a Menace: From Espionage to Exploitation
Coruna’s journey began in February 2025, when it was first identified as a state-of-the-art surveillance tool provided by private vendors to government clients. Its initial mission: precise monitoring of political figures and dissidents. By the summer of 2025, the narrative shifted as UNC6353, a hacker group with ties to the Russian government, seized control of the kit, deploying it for geopolitical espionage against Ukrainian citizens.
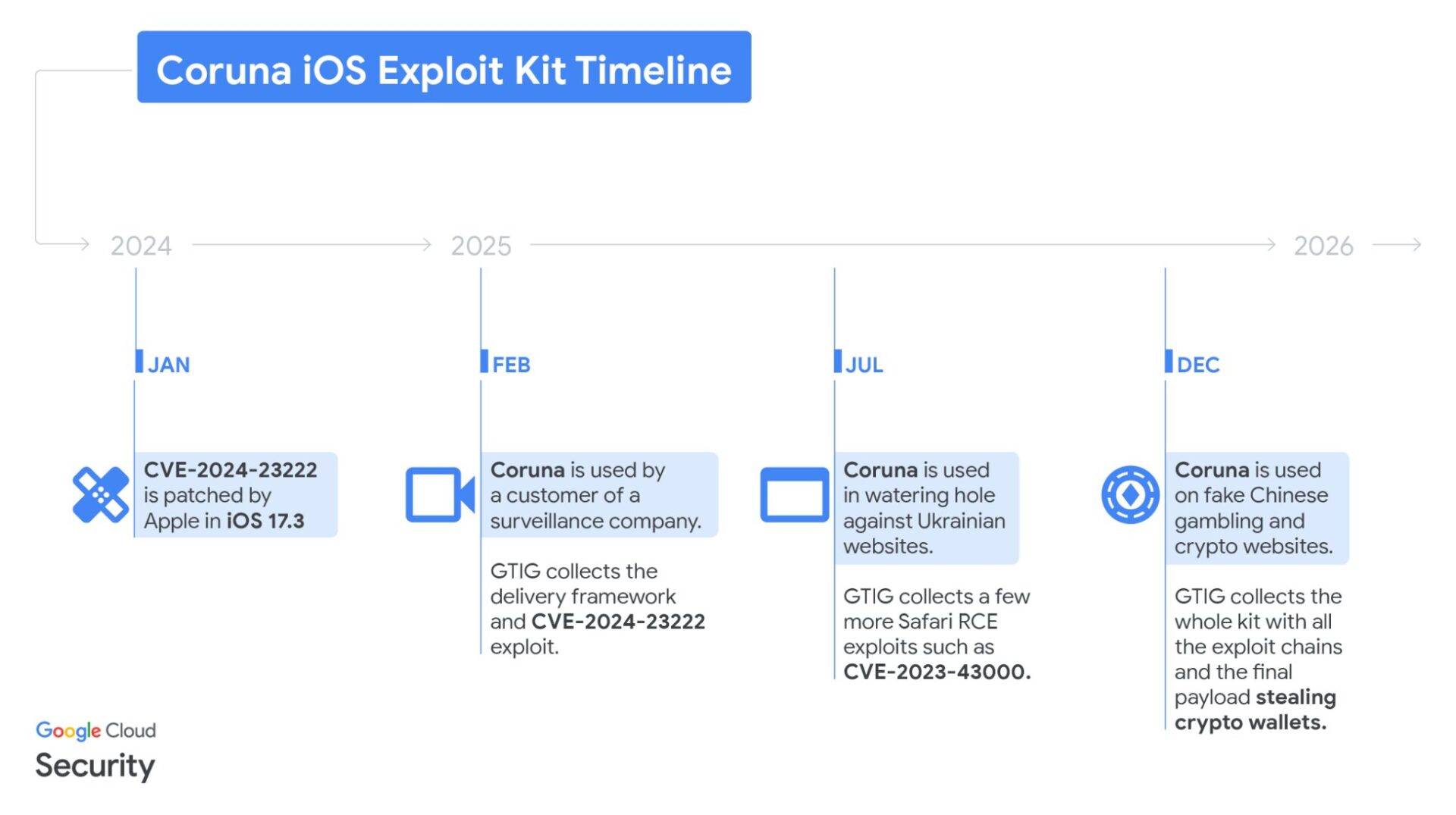
However, the most alarming development occurred in late 2025 to early 2026. This multi-million dollar, professional-grade tool leaked into the cybercrime underworld. A Chinese hacker organization, UNC6691, acquired the technology and pivoted its focus entirely towards the large-scale theft of digital assets. This marks a concerning commercialization of high-end spy tools, shifting from targeted intelligence gathering to indiscriminate wealth extraction from ordinary cryptocurrency holders.
Researchers emphasize that the hackers’ willingness to invest such substantial technical resources underscores the immense profits available in the cryptocurrency market, driving professional-grade technology directly into the hands of financial criminals.
Silent Infiltration: The 23-Vulnerability Chain Behind “Watering Hole” Attacks
The Coruna kit is renowned for its exceptional automation and stealth. It integrates 23 distinct vulnerabilities, forming five complete attack chains. Its broad reach encompasses all iPhone and iPad devices running iOS versions from 13.0 up to 17.2.1. The attackers employ insidious “watering hole attacks,” compromising legitimate cryptocurrency exchanges and financial websites or establishing sophisticated fakes to lure victims.
These fraudulent sites, like the counterfeit WEEX trading platform, are virtually indistinguishable from their official counterparts in both appearance and functionality. They even leverage search engine optimization (SEO) and paid advertisements to maximize their exposure and ensnare unsuspecting users.
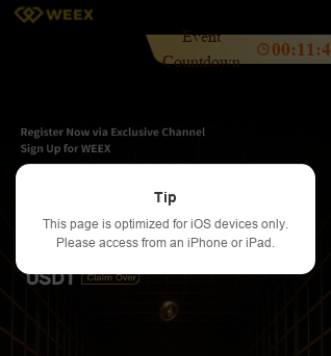
When an iPhone user visits one of these compromised web pages, a background script immediately identifies their device. The system silently checks the iOS version, and if it falls within the vulnerable range, a zero-click exploit is automatically triggered. This entire process requires no user interaction, no clicks, and no downloads. Some fake websites even proactively prompt users to browse with an iOS device, falsely claiming a “better experience,” solely to precisely target vulnerable devices running unpatched systems.
No Digital Stone Unturned: Even Screenshots Are at Risk
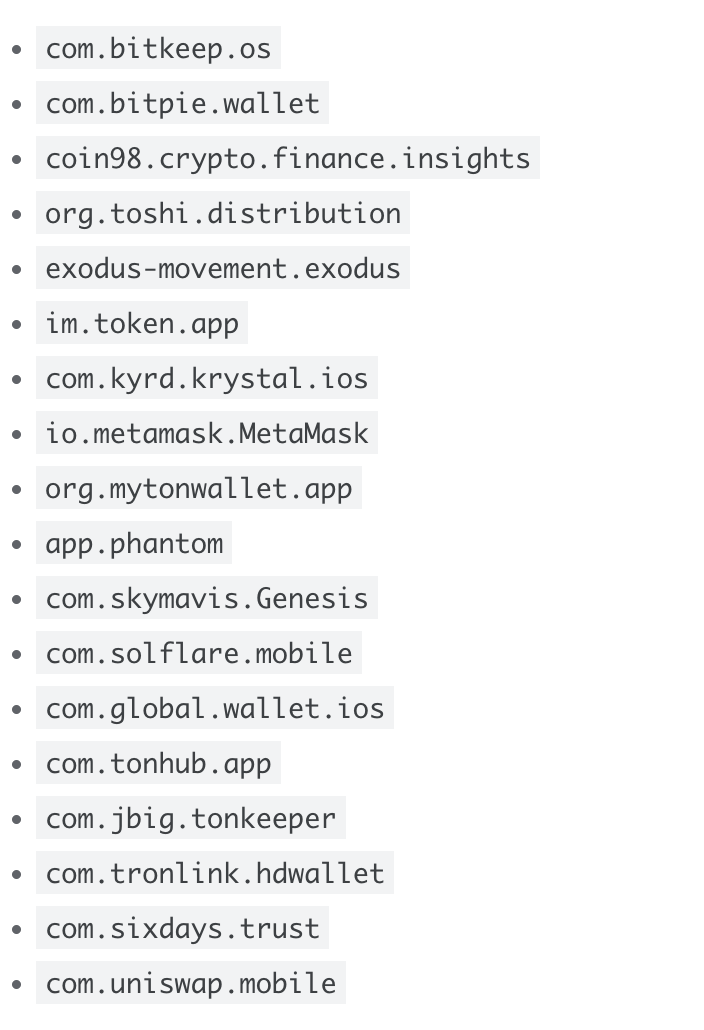
Once Coruna successfully gains device privileges, its malicious payload, PlasmaLoader, springs into action, meticulously inventorying the user’s digital assets. This program boasts powerful scanning capabilities, actively searching for specific keywords such as “backup phrase,” “bank account,” or “seed phrase” and extracting critical data from SMS messages and notes. Alarmingly, the kit also features advanced image recognition, allowing it to automatically scan users’ photo albums for screenshots containing wallet seed phrases or QR codes.
Beyond static data collection, Coruna aggressively targets popular cryptocurrency wallet applications like MetaMask and Uniswap. The hackers attempt to extract sensitive information from these apps to gain complete control over the wallets. In multiple documented cases, victims’ funds were transferred shortly after visiting a fraudulent website.
Given that the attack targets low-level system permissions, any private key that has left a digital trace on the phone, however fleeting, is vulnerable to this intelligence-grade harvesting tool.
Fortifying Your Digital Defenses: System Updates are Paramount
In the face of such sophisticated threats, iPhone users must adopt clear protective measures. Google’s report unequivocally states that Coruna is completely ineffective against iOS 17.3 or higher versions. While newer iOS versions are available, many users remain exposed due to outdated devices or insufficient storage preventing timely updates. For older models unable to upgrade to a secure version, enabling Apple’s “Lockdown Mode” offers an effective countermeasure; the malware is designed to cease operation upon detecting this mode to avoid tracking.
Cybersecurity experts advise cryptocurrency holders to adhere to fundamental survival rules. The primary defense is the use of hardware wallets (such as Ledger or Trezor), which keep private keys permanently offline and isolated from the iOS environment. Furthermore, immediately delete all screenshots containing seed phrases or private keys from your photo albums, opting instead for offline, physical backups.
While Coruna may avoid incognito browsing mode to reduce its chances of detection, this offers only a temporary and limited defense. As the value of digital assets continues to soar, maintaining up-to-date software and a vigilant cybersecurity posture has become a fundamental obligation for every investor.
(The above content has been excerpted and reproduced with authorization from our partner CryptoCity.)
Disclaimer: This article is for market information purposes only. All content and views are for reference only and do not constitute investment advice, nor do they represent the views and positions of BlockTempo. Investors should make their own decisions and transactions. The author and BlockTempo will not bear any responsibility for direct or indirect losses incurred by investors’ transactions.