By HIBIKI, CryptoCity
Quantum Threat to Bitcoin Accelerates: Google Simulates 9-Minute Heist
In a groundbreaking announcement on March 31, Google revealed that future quantum computers could crack the elliptical curve cryptography (ECC) protecting cryptocurrencies like Bitcoin with significantly fewer resources than previously thought. A simulated scenario demonstrated that a quantum computer with a fast clock speed could derive a Bitcoin private key from its public key in approximately nine minutes.
This revelation is particularly alarming for Bitcoin. Given that the Bitcoin network generates a new block every ten minutes on average, an attacker would have a crucial one-minute window. During this period, transactions awaiting confirmation in the memory pool (mempool) could be directly hijacked, potentially putting the entire Bitcoin supply at risk.
- Related Report: Quantum Threat Arriving Early? Google Simulates “9-Minute Bitcoin Heist” Scenario, 6.9 Million BTC at Risk
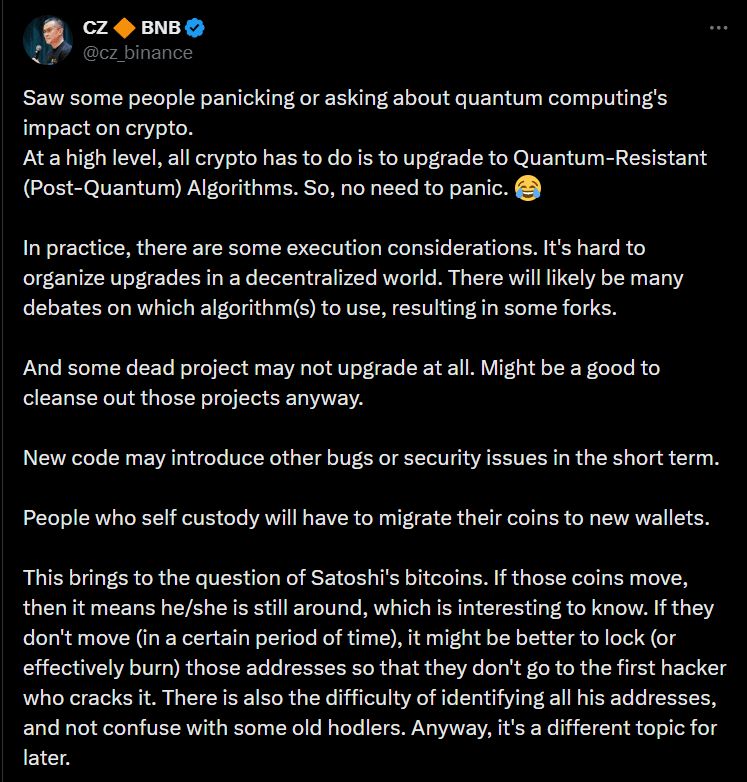
Binance CEO CZ Addresses Quantum Concerns: Industry Must Upgrade, No Need for Panic
Google’s findings quickly sparked widespread panic and debate within the crypto community. Binance founder Changpeng Zhao (CZ) promptly responded, asserting that the cryptocurrency industry simply needs to upgrade to quantum-resistant algorithms to mitigate the threat, and investors should not succumb to undue panic.
CZ acknowledged the practical challenges inherent in upgrading decentralized networks. He noted that disagreements over which algorithms to adopt could lead to network forks, and some dormant projects might fail to upgrade entirely—a situation he paradoxically viewed as an opportunity to “cleanse the market.”
Furthermore, CZ warned that the initial transition to new code could introduce new security vulnerabilities. Users who self-custody their assets would also be required to transfer their cryptocurrencies to new, quantum-resistant wallets.
Regarding early Bitcoin held by Satoshi Nakamoto, CZ suggested that any movement of funds from these addresses would draw significant attention. If Satoshi’s wallets remain inactive for an extended period, the community should consider locking or destroying these funds to prevent potential theft by future quantum attackers.
The Quantum Countdown: Why Bitcoin’s Ten-Year Buffer Has Vanished
Discussions around the quantum threat to Bitcoin are not new. However, the industry previously operated under the assumption of at least a decade of preparation time, with initial attack targets limited to dormant Bitcoin. Earlier research by CoinShares even suggested that only about 10,000 Bitcoins were genuinely at risk.
However, Alex Pruden, CEO of post-quantum cryptographic security firm Project Eleven, warns that Google’s latest article leaves the industry no room for complacency.
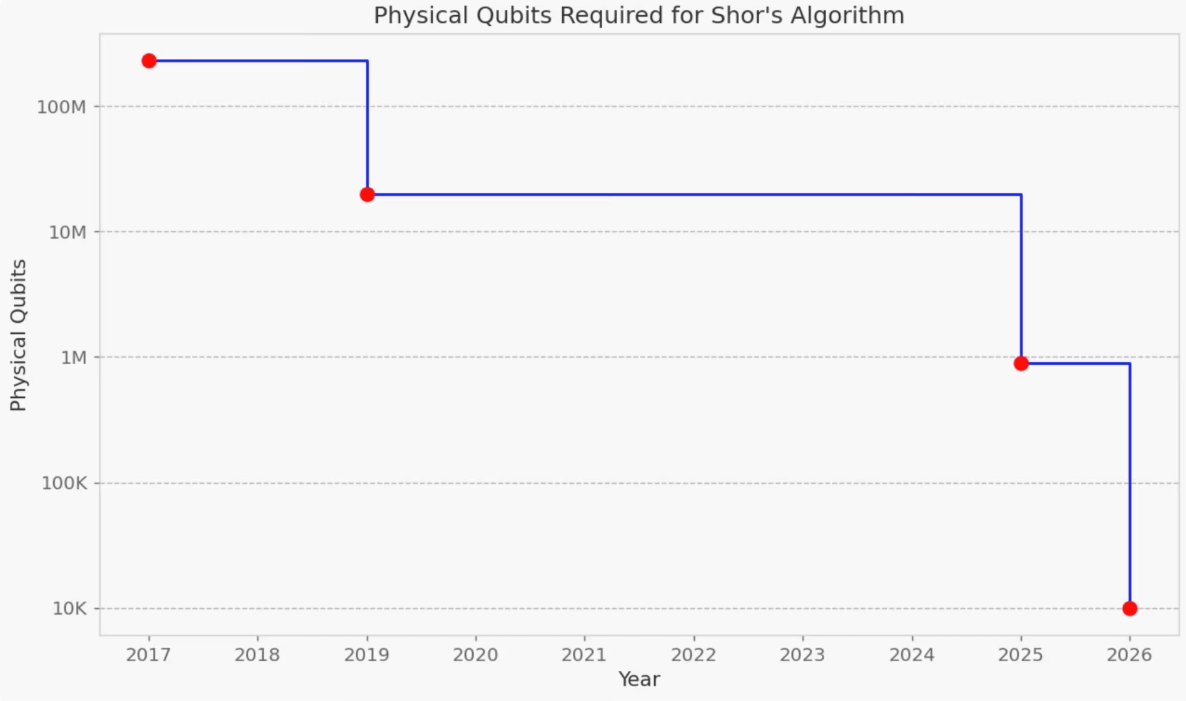
Past assessments were largely based on older algorithms like RSA-2048, which posited that tens of millions of physical qubits would be necessary to threaten Bitcoin. Google’s new architecture, specifically targeting Bitcoin’s 256-bit Elliptic Curve Discrete Logarithm Problem (ECDLP), dramatically reduces the required resources to fewer than 500,000 physical qubits.
Google’s breakthrough is not an isolated incident. Researchers at Oratomic have reported that by utilizing high-rate quantum Low-Density Parity-Check (qLDPC) codes, Shor’s algorithm could be executed at a cryptographically significant scale using only approximately 10,000 to 22,000 reconfigurable atomic qubits.
What once required millions of qubits has been reduced by several orders of magnitude in just a few years, a remarkable feat achieved simultaneously on two independent technological fronts.
Bitcoin’s Post-Quantum Transition: A Challenge Far Beyond Centralized Systems
In discussions surrounding the quantum threat, a common refrain is that “if Bitcoin is in danger, traditional banks will fare much worse.” However, Pruden emphasizes a critical distinction: upgrading a decentralized network like Bitcoin is fundamentally different from updating enterprise servers. It involves securing trillions of dollars in assets and requires the implementation of new cryptography at the network’s most foundational layer.
Post-Quantum Cryptography (PQC) solutions often necessitate larger digital signatures, which in turn increase bandwidth, storage, and computational demands. Implementing such an upgrade would require a hard fork, and achieving community consensus for this significant change promises to be a challenging process.
Even with consensus, given Bitcoin’s current transaction processing speed, migrating all network assets to post-quantum addresses could take several months. Waiting until a cryptographically significant quantum computer is publicly demonstrated before acting would undoubtedly trigger severe price volatility and a profound crisis of trust.
Despite these challenges, progress is being made. Blockchain company BTQ Technologies has already deployed Bitcoin Improvement Proposal 360 (BIP 360) on Bitcoin’s quantum testnet. This proposal introduces a pay-to-Merkle-root output type to defend against quantum attacks and has already attracted over 50 miners to participate in testing.
- Related Report: Bitcoin’s Quantum Defense Battle Begins! BTQ Testnet Deploys “BIP 360,” 50 Miners Rush to Test
Ethan Heilman, the security researcher behind the BIP-360 proposal, candidly admits that a full implementation of quantum-resistant technology for Bitcoin might still require seven years. This timeline is significantly later than Google’s own deadline for post-quantum cryptography (PQC) migration, which they have set for 2029.
Experts Urge Pragmatism as Google Champions Responsible Quantum Transition
Pruden emphasizes that his arguments are not intended to spread panic but to urge major institutional Bitcoin holders, stablecoin issuers, and other key players to seriously confront these risks. The quantum threat has evolved from an academic theory into an engineering reality, necessitating a proactive global migration strategy and upgrades initiated well before the first quantum hack occurs.
Google, for its part, has disclosed that it collaborated with the U.S. government when revealing its research. This partnership focused on developing methods to describe vulnerabilities using zero-knowledge proofs. This mechanism allows third parties to verify claims without inadvertently providing malicious actors with an attack blueprint.
Google urges other organizations to adopt similar standards and looks forward to collaborating with institutions such as cryptocurrency exchange Coinbase and the Stanford Blockchain Research Center, aligning with its 2029 timeline to collectively drive responsible quantum solutions.
(The above content is an excerpt and reproduction authorized by our partner CryptoCity)
Disclaimer: This article is for market information purposes only. All content and opinions are for reference only, do not constitute investment advice, and do not represent the views and positions of BlockTempo. Investors should make their own decisions and trades. The author and BlockTempo will not bear any responsibility for direct or indirect losses resulting from investor transactions.