Author: Karl Marx OnChain
Compiled by: Yuliya, PANews
The decentralized finance (DeFi) sector has been plagued by staggering losses, with a reported $1.029 billion in 2024, $649 million in 2025, and an additional $137 million stolen in just the first quarter of 2026. PANews Note: DeFi losses have exceeded $600 million since April 2026 alone.
Why do these attacks persist, and why do we repeatedly overlook the same critical warning signs? Beneath the surface of these vulnerabilities, a clear pattern emerges: they are far from random occurrences.
This comprehensive analysis delves into the underlying patterns of major DeFi security incidents and highlights easily missed early warning signals. Drawing insights from over a hundred attack case studies, this article concludes with essential prevention strategies to navigate the complex landscape of Web3 security.

Unmasking Vulnerabilities: The Truth Behind Frequent Exploits
Before diving into specific incidents, it’s crucial to understand why we categorize these vulnerabilities into distinct classes. Fundamentally, DeFi failures often manifest at specific layers of a system, and each layer collapses in inherently different ways:
- Code Layer: Failures occur when underlying assumptions are not rigorously enforced. There might be no obvious logical errors, but edge cases, constraints, or invariants are never fully verified.
- Infrastructure Layer: This layer fails when trust is inadvertently placed in systems that are susceptible to compromise or misuse.
- Business Logic Layer: Here, the very “rules of the game” become the attack vector, where the system is exploited by following its own intended logic.
Below is a structured summary of typical cases across these vulnerability categories:
1. Infrastructure: Correct Control, Wrong Context
Infrastructure vulnerabilities arise not from stolen keys, but from the exercise of power without complete contextual awareness. Across numerous security incidents, a consistent pattern emerges: the correct individual signs a transaction, using the correct permissions, and the system operates precisely as designed.
Yet, funds are still lost. This happens because the system validates authenticity, not intent. A valid signature merely proves *who* signed, not whether they truly *understood* what they were signing. This critical gap between verification and comprehension is fertile ground for infrastructure collapse.
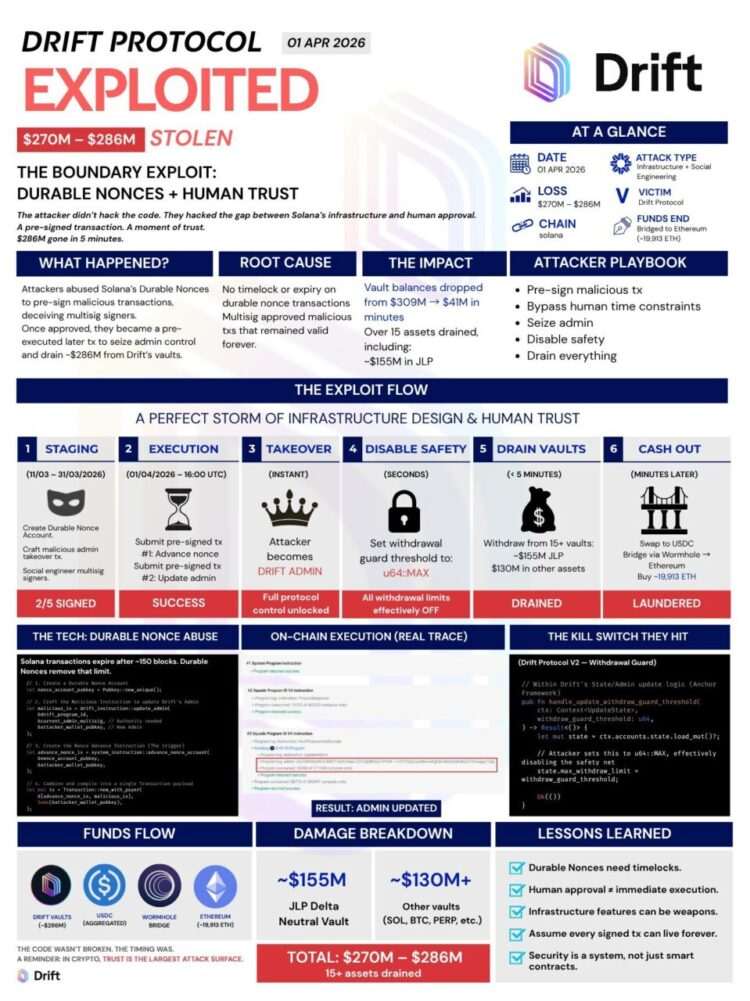
@DriftProtocol: The Premature Signature
The transaction was valid, and the signature was authentic. The team simply didn’t anticipate it would be used much later. It was approved during a routine check, with no immediate action. Then, one day, it was executed. Nothing was forged or altered.
The problem was straightforward: they signed something without controlling *when* it would be utilized.
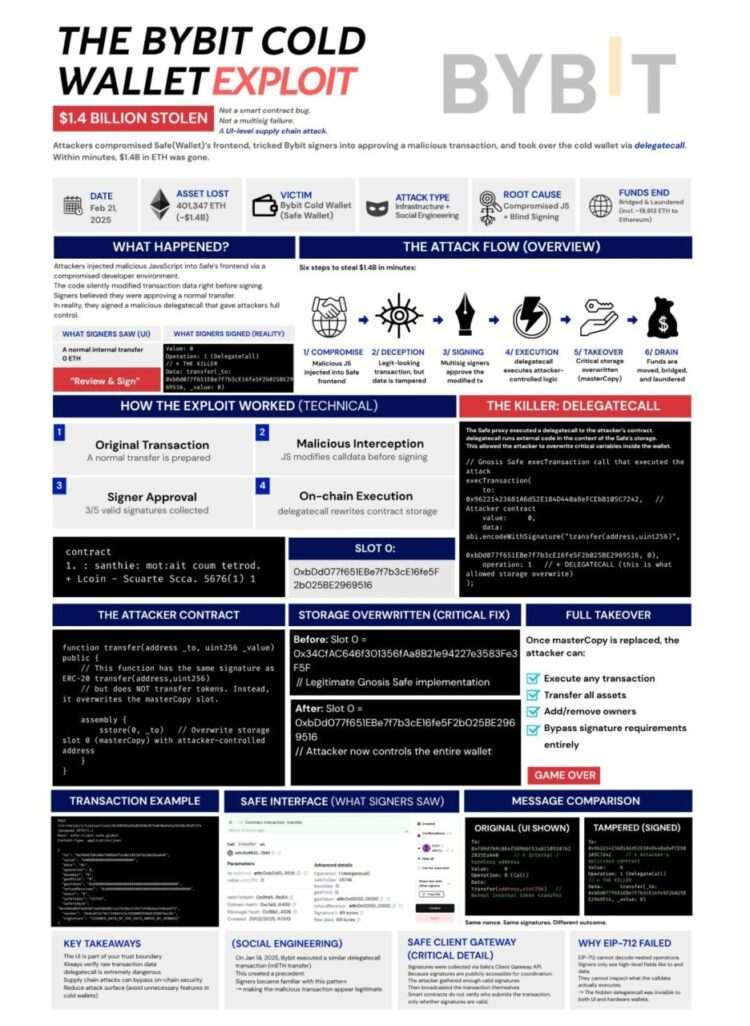
@Bybit_Official: Signing the Unseen
The system functioned correctly, and the signature was valid. Individuals simply signed something different from what they perceived. They saw a standard transfer and approved it. However, beneath the surface, the transaction was altering wallet control. In the conventional sense, nothing was “hacked”; all rules were followed.
The problem was simple: what they *saw*… was not what they *signed*.
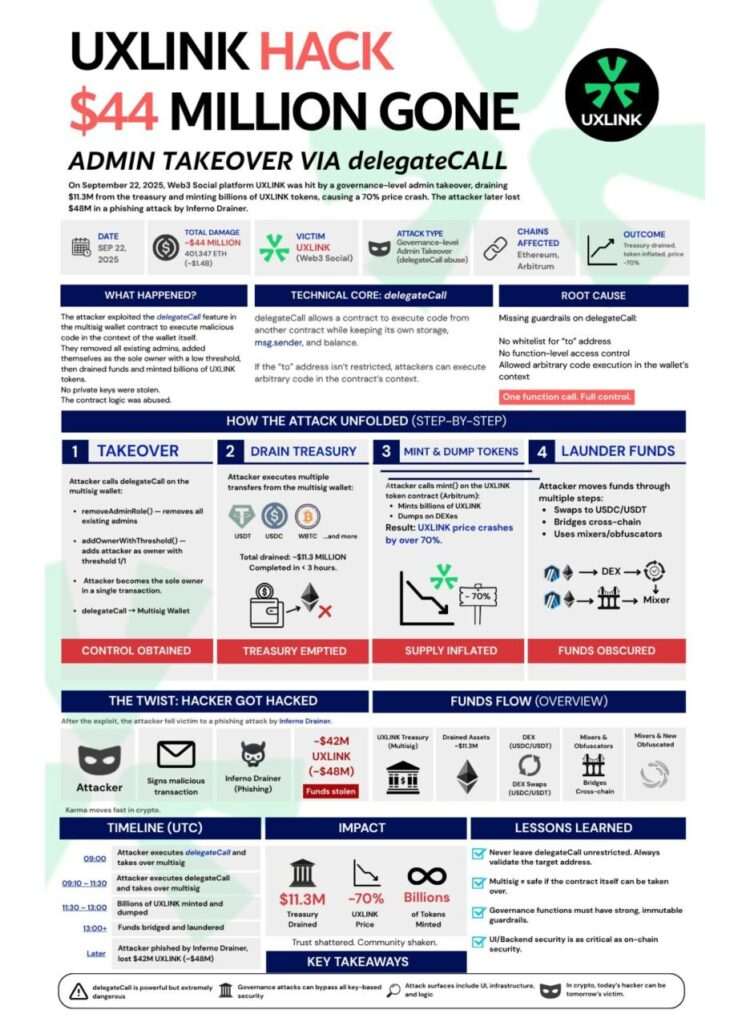
@UXLINKofficial: Authorized Misuse of Power
The system allowed the action, and the permissions were valid. No keys were stolen, and no checks were bypassed. Administrator roles were changed, and ownership was reallocated. All of this was accomplished through legitimate calls, with the system operating exactly as designed.
The problem was clear: the system granted sufficient power and implicitly trusted that it would not be abused.
2. Code: Where Assumptions Fail to Be Enforced
Code vulnerabilities rarely stem from obvious bugs. Instead, they often arise from systems that operate as expected, but only under specific, rather than *all*, conditions.
- Rules may exist, but they are not universally enforced across all pathways.
- Edge cases are overlooked until maliciously triggered by an attacker.
- Mathematical formulas work flawlessly in theory but crumble during code implementation.
- Security checks cover anticipated execution paths but fail to account for actual attack vectors.
In essence, the code fails precisely where its underlying assumptions no longer hold true.
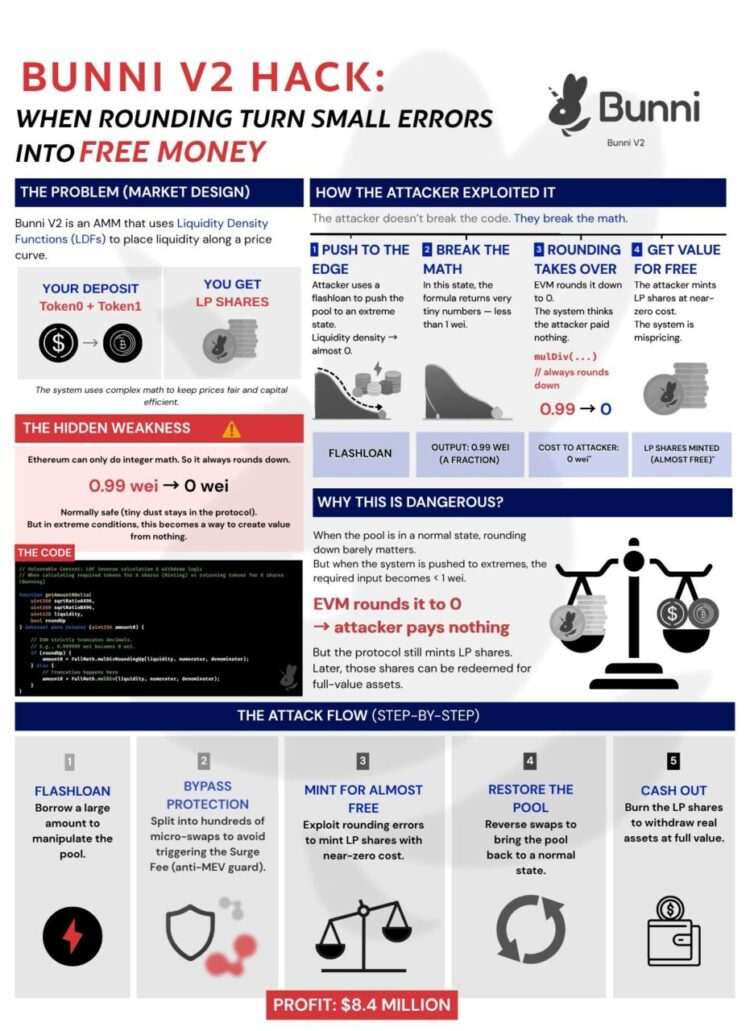
Bunni: Mathematical Precision Lost in Code
The system underwent an audit, confirming the code’s correctness. The model made perfect sense on paper: liquidity, pricing—everything checked out. However, in practice, minute rounding errors emerged. Instead of canceling each other out, they accumulated. The attacker didn’t break the system; they merely exploited its repetitive nature, over and over.
The problem was simple: the mathematical theory was sound, but the code implementation lacked precision.
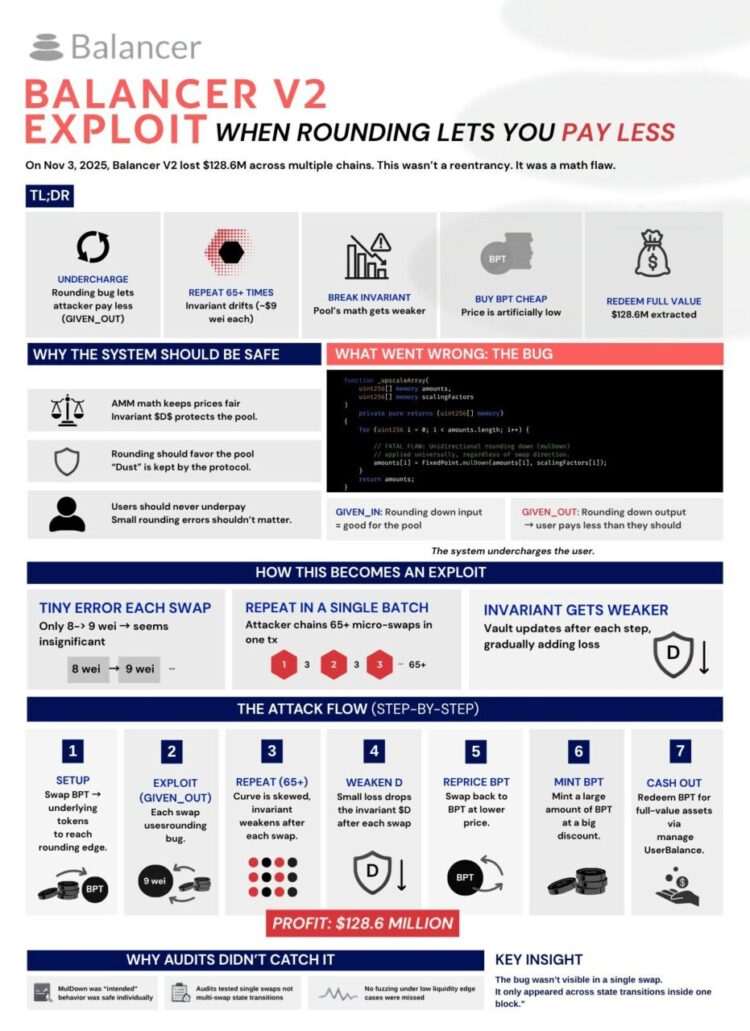
@Balancer: The Compounding Minor Flaw
The system operated normally, and the mathematical calculations were correct. Each transaction incurred an infinitesimally small, almost negligible, rounding loss. But this loss didn’t reset; it accumulated. The attacker didn’t exploit it once; they leveraged it multiple times within a single process.
The problem was clear: a small error, if repeated often enough, can snowball into a significant exploit.
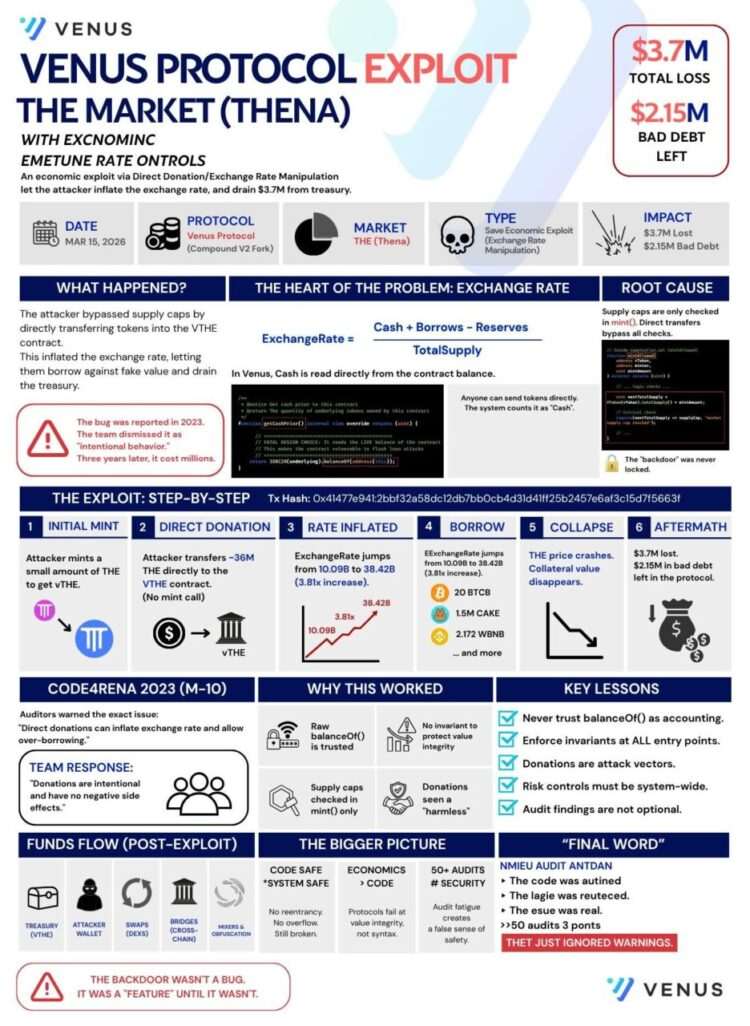
Venus: Rules Without Universal Enforcement
The system had a limit, and a checking mechanism was implemented. But it was present in only one specific location. Through an alternative path, the same rules did not apply. The attacker didn’t bypass the system; they simply bypassed that particular checkpoint.
The problem was straightforward: a rule that is not enforced everywhere is, effectively, no rule at all.
3. Business Logic: When the System Trusts the Wrong Inputs
In these scenarios, the system diligently follows its own rules, often placing implicit trust in external data like price feeds. If a price rises, for instance, the system allows for more borrowing.
Attackers exploit this by purchasing their own assets, artificially inflating the price. The system then “believes” they are wealthy, enabling them to borrow real, valuable assets. They then cash out. Nothing is “broken” in the code; the system simply trusts something that is easily manipulated.
Mango: The Illusion of Wealth
The system operated on a simple premise: higher prices lead to more collateral, which in turn allows for greater borrowing. The attacker purchased a large quantity of a low-liquidity token, causing its price to soar. They then used this artificially inflated price to borrow substantial real assets from the protocol. Subsequently, they ceased supporting the price, leading to a crash. The collateral became insufficient, but the borrowed funds were already gone.
No code was hacked; the system simply believed a manipulable price.

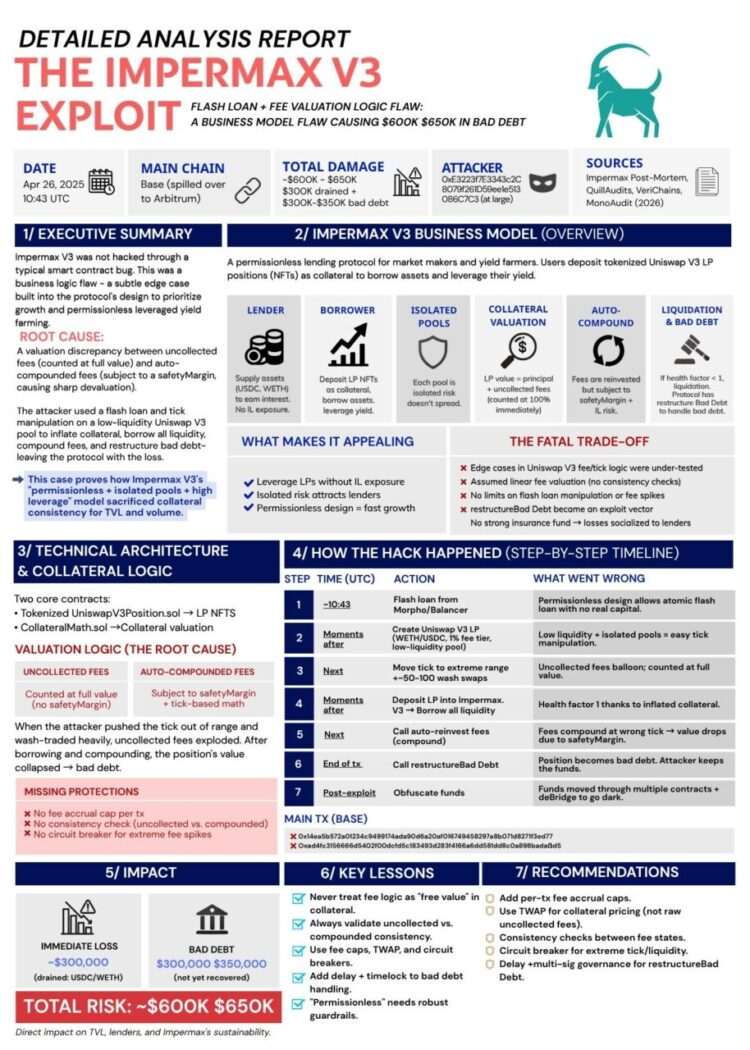
Impermax: The Fragile Price Mechanism
The system trusted the price, but the underlying market was too thin and illiquid. An attacker borrowed tokens and then traded against a low-liquidity pool. This caused the price to fluctuate wildly, far beyond its true value. The system then deemed the position unsafe and triggered a forced liquidation. The attacker had strategically set this up and profited from the forced sale.
Nothing was broken; the price was simply too easily manipulated.
The Ultimate Lesson: How to Survive and Thrive in DeFi
Across all these vulnerabilities, one critical truth emerges: you don’t need to make a mistake to lose money; you merely need to be exposed to risk when a system inevitably falters.
The core issue isn’t that protocols are inherently broken, but rather that they rely on elements prone to error: assumptions, external context, or volatile prices. Therefore, our objective isn’t to seek a perfectly infallible system, but to meticulously control the degree of trust we place in them.
In practice, this means:
- Question Everything: Do not blindly trust what you see on a user interface. Verify critical information independently.
- Assumptions Are Risks: Never assume that rules or safeguards will always protect you in every conceivable scenario.
- Price Is Not Absolute: Do not treat price feeds or advertised yields as absolute, immutable truths. Understand their potential for manipulation.
- Diversify & Decentralize: Avoid exposing all your assets in a single location or protocol, as failures often occur rapidly and without prior warning.
Survival in DeFi ultimately boils down to effective damage limitation: utilize systems that rigorously enforce constraints, steer clear of setups that are easily manipulated, and always retain the ability to exit your positions promptly.
In the world of decentralized finance, you cannot win by blindly trusting systems; you can only survive by meticulously controlling how much they are capable of harming you.
(The above content is an authorized excerpt and reproduction from our partner PANews. Original Article Link)
Disclaimer: This article is for market information purposes only. All content and opinions are for reference only and do not constitute investment advice. They do not represent the views or positions of BlockTempo. Investors should make their own decisions and trades. The author and BlockTempo will not be liable for any direct or indirect losses incurred by investors’ transactions.